The Hidden OT Risk in Your Quality Labs
Quality labs stuck between a rock (IT) and a hard place (OT)
The Hidden OT Risk in Your Quality Labs
Does this sound like your quality lab?
Quality labs are another oft ignored blind spot in manufacturing cybersecurity. Sitting between IT and operational technology, these environments house million-dollar analytical instruments, critical test data, and access pathways that could compromise both enterprise networks and production systems. Yet they remain largely unprotected, caught in the security silo between IT teams focused on corporate networks and OT teams protecting production lines.
A critical gap exists in how manufacturers approach lab security. Recent studies indicate that 84% of manufacturers have embraced or are actively considering smart manufacturing applications, yet lab systems often connect to networks without proper security controls. My own assessments have discovered lab equipment accidentally bridged between OT and corporate networks, creating unintended pathways for lateral movement. Many analytical instruments ship with default passwords and un-encrypted communications as standard, vulnerabilities that would be unacceptable in any modern IT system but persist in million-dollar lab equipment.
Oh not the convergence word again…
The manufacturing industry is experiencing accelerating IT/OT convergence. Omdia’s recent research found that 80% of manufacturers experienced increased cyber incidents, yet only 45% feel adequately prepared to defend against these threats. More concerning: the study revealed a “fragmented approach to security responsibility” with a lack of clear ownership and authority for securing mission-critical systems and quality labs epitomize this exact problem.
When IT and OT teams operate independently, labs hide under the radar with equipment that is treated like OT because it can’t be easily upgraded or replaced. As detailed in the ISA OT Cybersecurity Summit analysis, three primary definitions of IT/OT convergence each create distinct security risks. The most dangerous scenario for labs is when IT management practices are enforced directly onto OT infrastructures without understanding the validation and operational requirements unique to analytical environments. IT security teams apply standard patching schedules that could invalidate instrument certifications. OT teams, focused on production continuity, overlook the enterprise connectivity risks that lab equipment now presents.
Why Quality Labs Matter to Your Supply Chain Risk
Quality labs generate data that often bridges operational and enterprise systems through pathways most organizations don’t monitor or control. The convergence of IT and OT systems is driving manufacturing innovation, but organizations that fail to adopt intentional integration strategies risk leaving their labs in a vulnerable state. Lab equipment connects to:
Enterprise networks – for data reporting, regulatory compliance uploads, and remote vendor diagnostics
Production systems – for real-time quality feedback and feed-forward controls
Third-party infrastructure – for cloud analytics, vendor support, and regulatory submissions
But the connectivity threat extends far beyond network connections. Many quality labs still operate legacy workstations running Windows XP, Windows 7, or even Raspberry Pi OS, some of which haven’t received security patches in years. These aging machines collect critical test data from million-dollar analytical instruments, yet they remain largely invisible to corporate IT security programs because they’re perceived as “OT” systems outside IT’s scope.
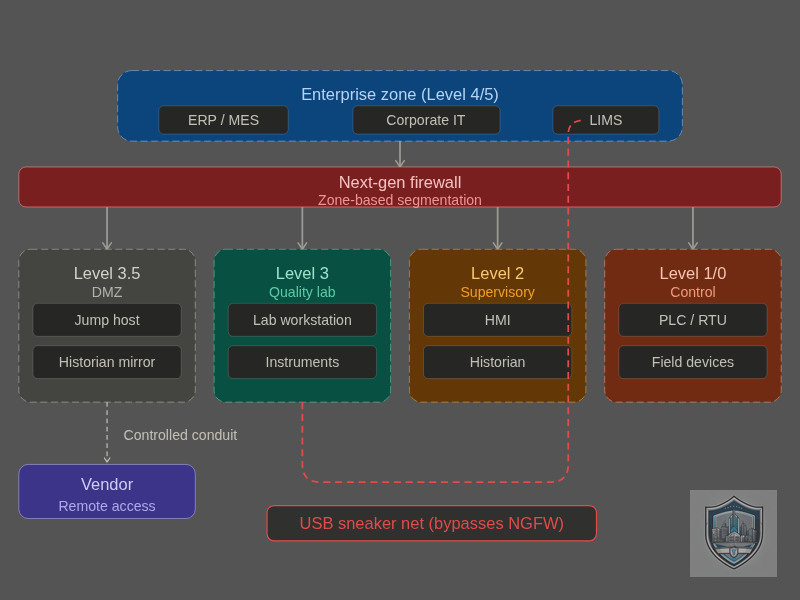
The real vulnerability emerges in how data moves between these domains. We’ve documented cases where lab technicians download test data to USB drives and then plug those same drives directly into corporate assets for reporting and regulatory submission. This “sneaker net” approach creates a direct bridge between isolated lab environments and enterprise networks—a pathway that can carry not just data, but malware, configuration changes, and persistent threats. A compromised USB drive becomes a vector that bypasses all network segmentation, firewalls, and perimeter controls.


Each connection point—whether networked or physical—is a potential entry vector for compromise. Default credentials on a spectrophotometer. Un-encrypted data flows from a chromatograph. Remote access sessions from equipment vendors. USB-based data transfer from decades-old workstations to modern corporate systems. All of these are routine in quality labs, and all represent security risks that span both IT and OT domains, creating bridges that traditional security models fail to address.
The Third-Party Vendor Problem
Quality lab equipment typically requires ongoing support from manufacturers. Some vendors need remote access to perform diagnostics, install updates, and validate system performance. Others require yearly onsite visits during calibrations to apply patches and upgrade equipment. This creates a practical security challenge: how do you enable necessary vendor access while preventing that access from becoming a persistent backdoor?
Traditional IT solutions (VPNs, SSH sessions, application firewalls) weren’t designed for the constraints of analytical equipment. OT-style air-gapping or strict network isolation breaks vendor support arrangements and may violate service level agreements. Labs sit in this uncomfortable middle ground where neither traditional IT nor traditional OT security solutions work perfectly.
Breaking Down the Silos
Breaking down silos between IT, OT, and quality organizations is essential. Lab security is not just an IT problem or an OT problem—it’s an enterprise risk that demands coordinated response. By applying proven OT security frameworks while respecting the unique operational requirements of analytical environments, manufacturers can close this critical security gap.
The path forward requires:
Acknowledging the problem – Quality labs are OT assets that require OT security discipline, not IT afterthoughts
Clarifying ownership – Establish clear accountability for lab security across IT, OT, and quality organizations
Understanding constraints – Recognize that labs have validation requirements and operational continuity needs that shape what security controls are feasible
Implementing segmentation – Separate lab networks from both enterprise and production infrastructure with controlled data flows
Managing vendor access – Audit, document, and control third-party access with compensating controls where traditional solutions don’t fit
Partner with DirectDefense for Comprehensive OT Security
At DirectDefense, we’ve helped manufacturers across industries identify and remediate vulnerabilities in their quality lab environments. Our approach combines deep OT security expertise with an understanding of the unique challenges these environments present—from validation constraints to vendor management complexities.
Our OT security assessment methodology specifically addresses quality lab risks through:
Comprehensive asset discovery including legacy analytical equipment and sneaker net data flows
Network traffic analysis to identify improper segmentation and unauthorized communications
Vendor access audit and remediation planning with focus on shared credential risks
Custom security roadmaps that balance operational needs, regulatory requirements, and risk reduction
Practical compensating controls for systems that cannot be traditionally secured
Quality labs are critical to your manufacturing operation and your supply chain integrity. Don’t leave them as the overlooked vulnerability in your OT security program. Reach out to schedule an assessment.